Warning
You are looking at documentation for an older release. Not what you want? See the current release documentation.
SAML2 is version 2 of SAML (Security Assertion Markup Language), an XML-based standard for exchanging authentication and authorization data. The document of SAML2 Specifications is available here.
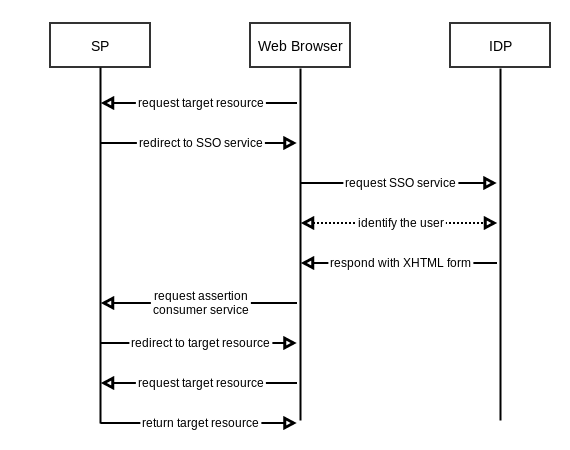
According to SAML2 Specifications, two parties which exchange authentication and authorization data are called SP (Service Provider) and IDP (Identity Provider). IDP issues the security assertion and SP consumes it. The following scenario describes a SAML2 exchange:
A user, via web browser, requests a resource at the SP.
The SP checks and finds no security context for the request, then it redirects to the SSO service.
The browser requests the SSO service at IDP.
The IDP responds with an XHTML form after performing security check and identifying the user. The form contains SAMLResponse value.
The browser requests assertion consumer service at the SP.
The consumer service processes the SAMLResponse, creates a security context and redirects to the target resource.
The browser requests target resource again.
The SP finds a security context, so it returns the target resource.
In this document, two addresses, www.sp.com and www.idp.com, and folders with name $PLATFORM_* are used to respectively represent URLs and home folders of SP and IDP.
eXo Platform can perform both roles SP and IDP; thus, it can integrate with services like Salesforce and Google Apps.
Note
SAML2 IDP integration only works for eXo Platform on Jboss.
SAML2 SP integration works for eXo Platform Jboss and Tomcat.
This chapter covers the following subjects: